Overview
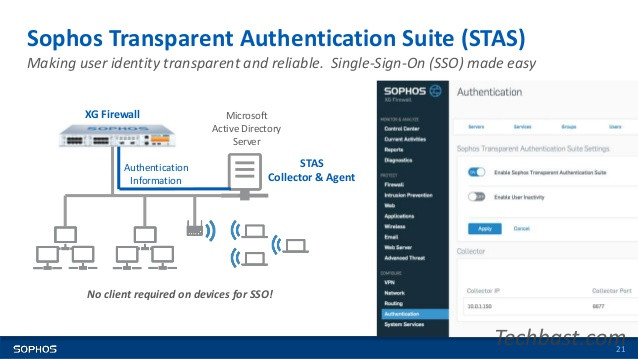
Sophos Transparent Authentication Suite eliminates the need to remember multiple passwords when users log into Sophos UTM when he log in to Windows with his password username and password. In addition, it removes SSO client settings on each workstation. Easy to use for end users and a higher level of security in addition to reducing operating costs related to client installation
The article will show you how to integrate STAS in an environment with an Active Directory Server on the Sophos XG firewall device
How to configure
Step 1: Configure ADS
Configuration on Active Directory
- Start -> Administrative Tools -> Local Security Policy to view the security settings
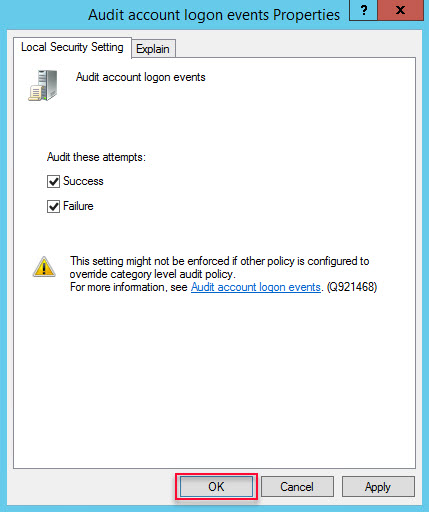
- Go to Security Settings -> Local Policies -> Audit Policy -> Audit account logon -> Right clock Audit account logon events -> Select Properties
- Select both Success and Failure items -> Click OK
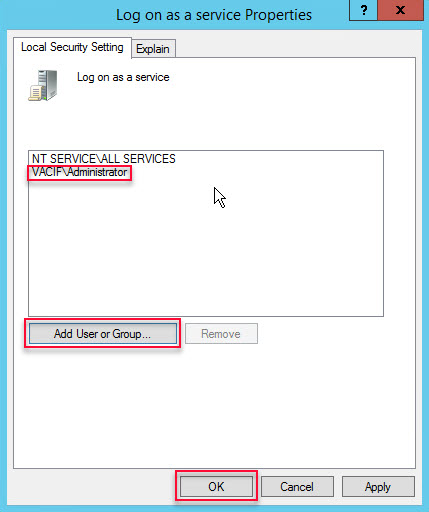
- Local Security Policy -> Security Settings -> Local Policies -> User Rights Assignment -> Log on as a service -> Right click Log on as a service -> Select Properties
- Click Add User or Group -> Add user administrator -> Click OK
Step 2: Download STAS
- Log into AD with Administrator account
- Log in to the graphical interface of Sophos XG with an Admin account
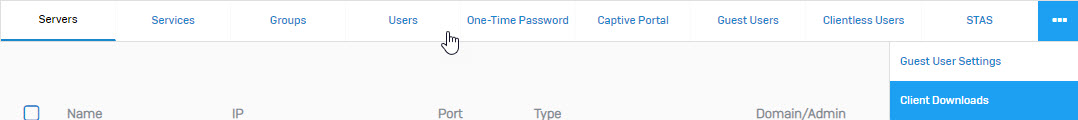
- Authentication -> Click on the icon … -> Select Client Download to download the installation file -> Install on AD Server
- You can also download STAS from the Download Client page in the User Portal when logging in with an Admin account
Step 3: Install STAS on AD
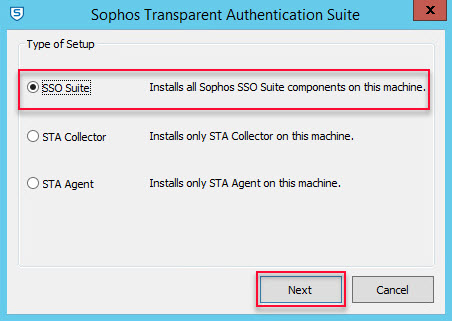
- Install the downloaded STAS. Click Next 4 times -> Click Install
- Select SSO and click Next
- Enter admin’s username and password -> Click Next
- Click Finish to complete the instalation
Step 4: Configuration for STAS
- Open STAS by double clicking on the Sophos Transparent Authentication Suite on the desktop
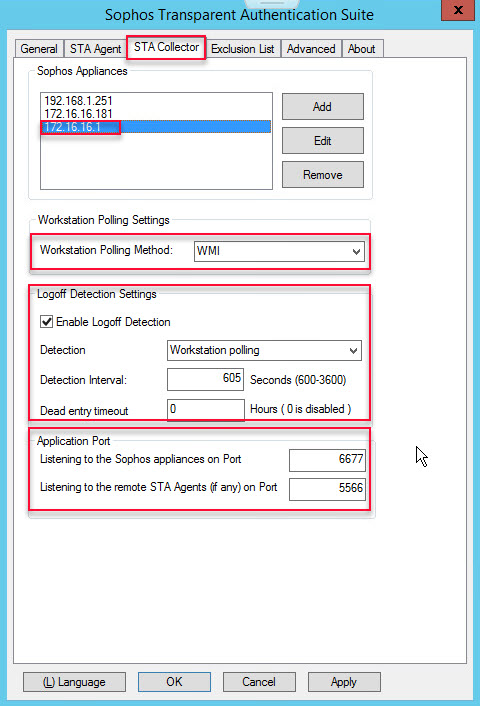
- On the STA Collector tab
- In Sophos Appliances section -> Click Add to add the IP of the LAN port of the Sophos XG device
- At Workstation Polling Settings: Select WMI
- In the Logoff Detection Settings section and Appliance Port -> Keep the default configuration
-> Click Apply
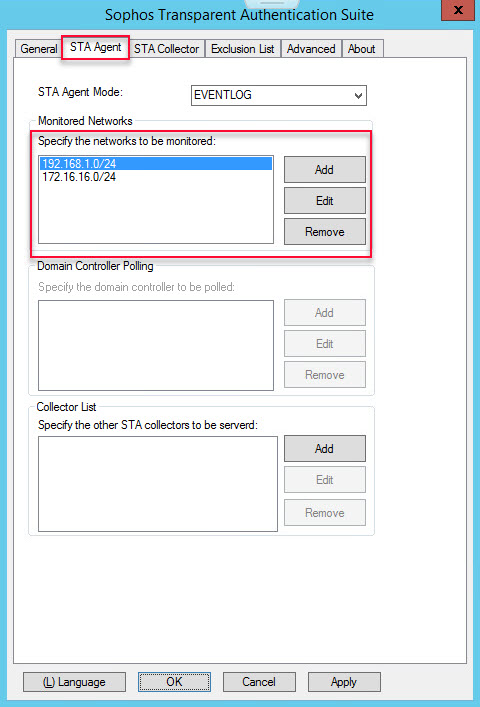
- On the STA Agent tab
- In Monitor Networks -> Click Add to add the LAN Network you want to authenticate
-> Click Apply
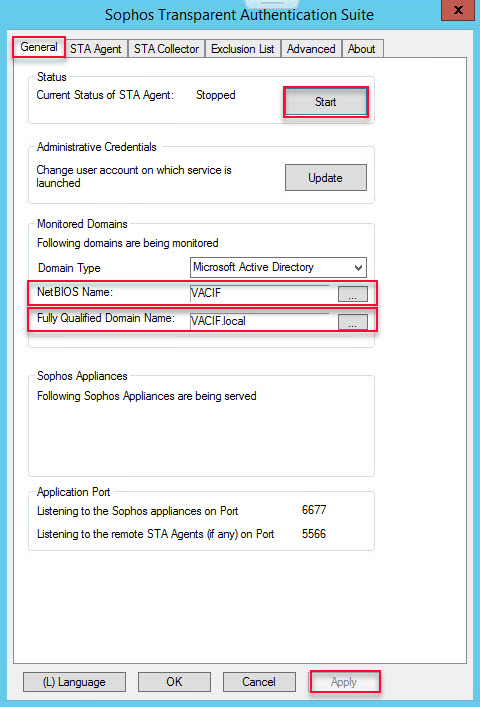
- On the General tab
- Enter the NetBIOS name of the domain
- Enter the FQDN of the domain
- Click Start to start STAS
-> Click Apply -> Click OK
Step 5: Add AD Server to Sophos XG to authenticate domain user
Configuration on XG
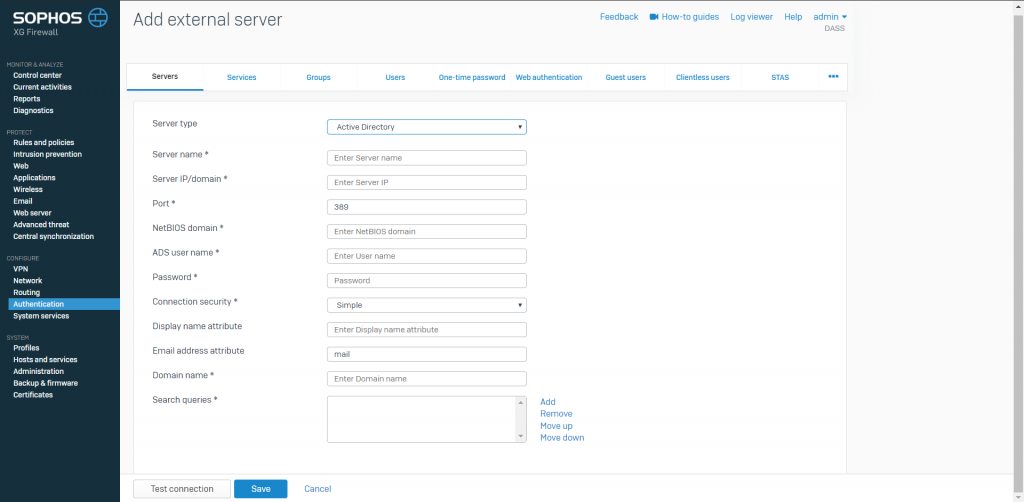
Authentication -> Servers -> Click Add
- In the Server type section: Select Active Directory
- Server name: Name the server you want to manage
- Server IP/domain: Enter the IP of AD
- Port: 389
- NetBIOS domain: Enter the NetBIOS name of AD
- ADS username: Enter the administrator
- Password: Enter the password of the administrator account
- Connection security: Select Simple
- Display name attribute: Enter the name for the server you want to manage
- Email address attribute: Enter the email you want (can be left blank)
- Domain name: Enter your domain name
- Search queries: Enter domain name in queries (Ex: dc=vacif,dc=com)
-> Click Test connection -> Click Save
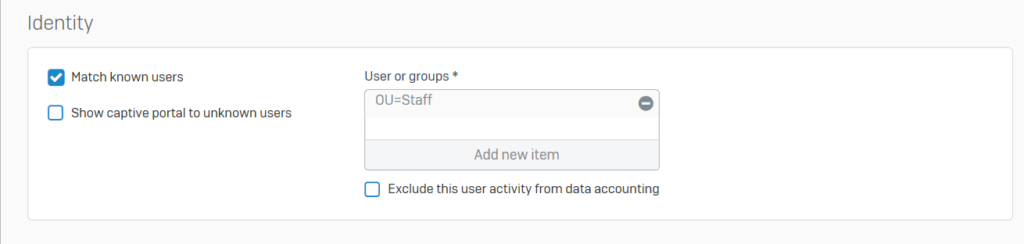
Step 6: Adjust Service configuration to firewall authentication with AD server
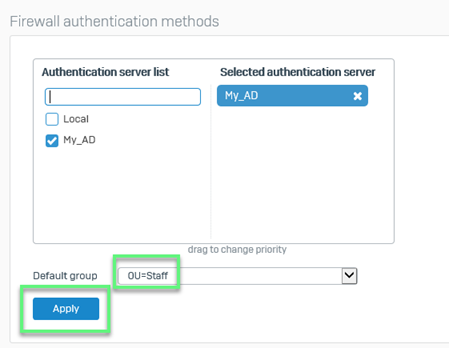
Authentication -> Services
In the Firewall authentication methods section
- Click on your AD and uncheck Local
- In the Default group section: Select the OU you have added
-> Click Apply
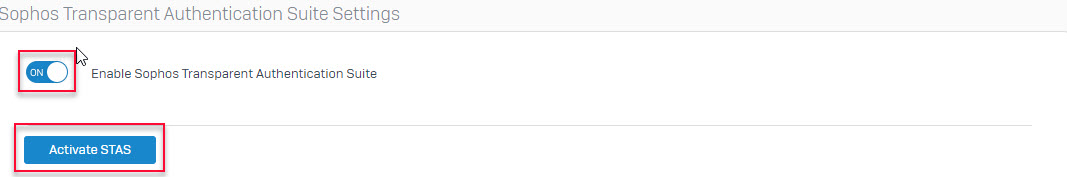
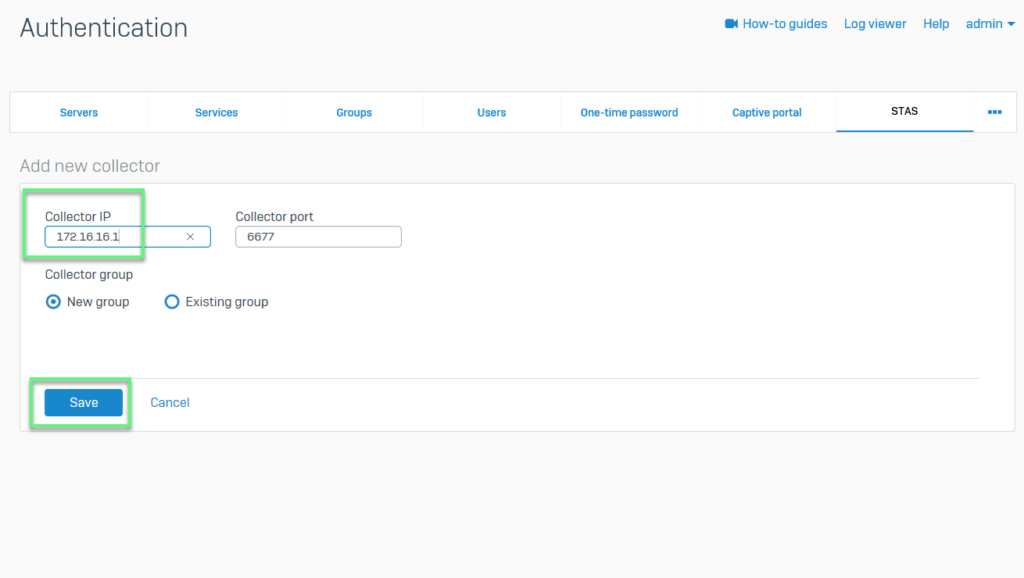
Step 7: Configure STAS on XG Firewall device
- Authentication -> To turn on STAS by selecting ON and press Active STAS
- After activate, choose Add New Collector
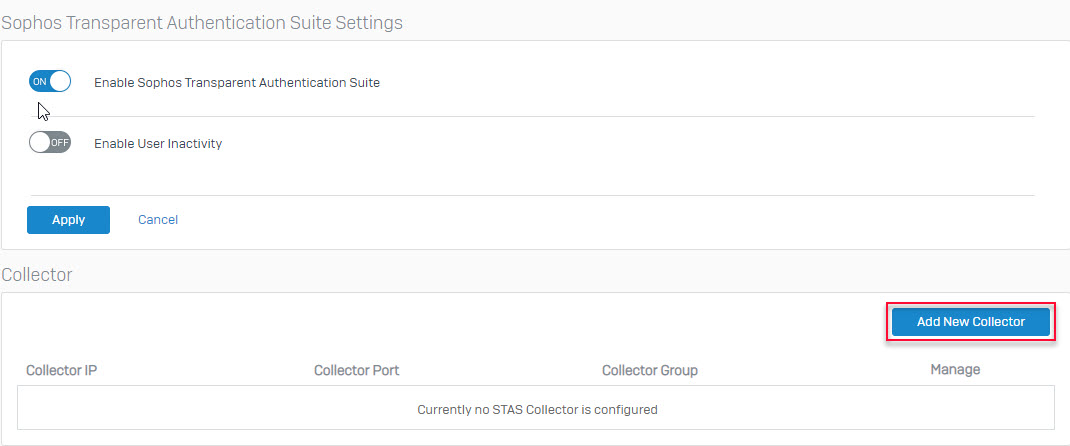
- Enter the IP of AD Server in Collector IP -> Click Save
Step 8: Create firewall rule to using authentication STAS
- STAS -> Click Add Firewall rule to create firewall rules, control traffic by user
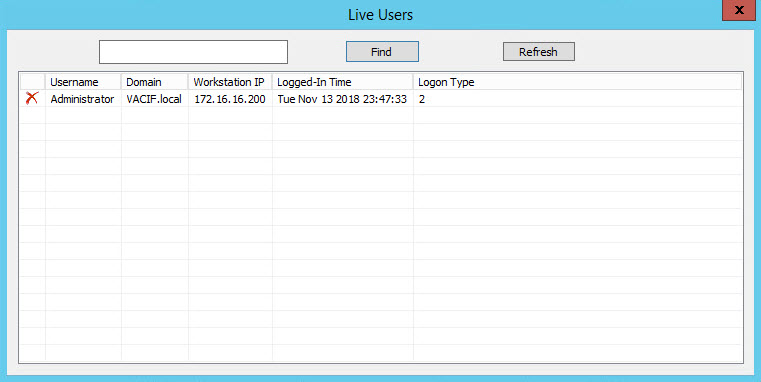
Step 9: Verify user
Leave a Reply